Appendix A.pdf - AlienVault I.T Security Vulnerability Report Job Name Michael.Roberts.scan.1192021 Scan time 20:08:57 Profile Default Non destructive | Course Hero
What Really Matters When Selecting a SIEM and How to Choose a SIEM Looking into the Correlation? | PeerSpot
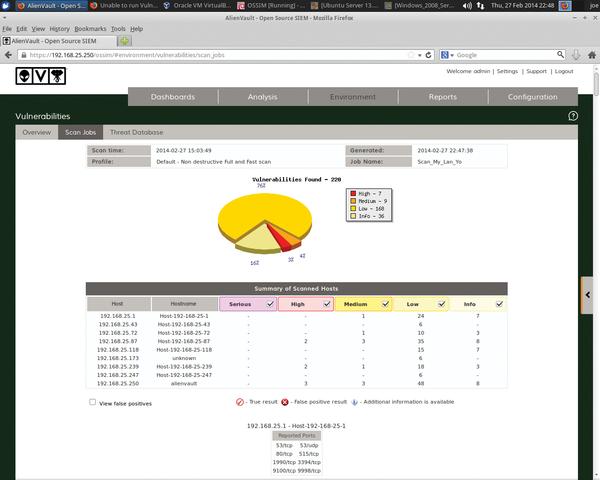
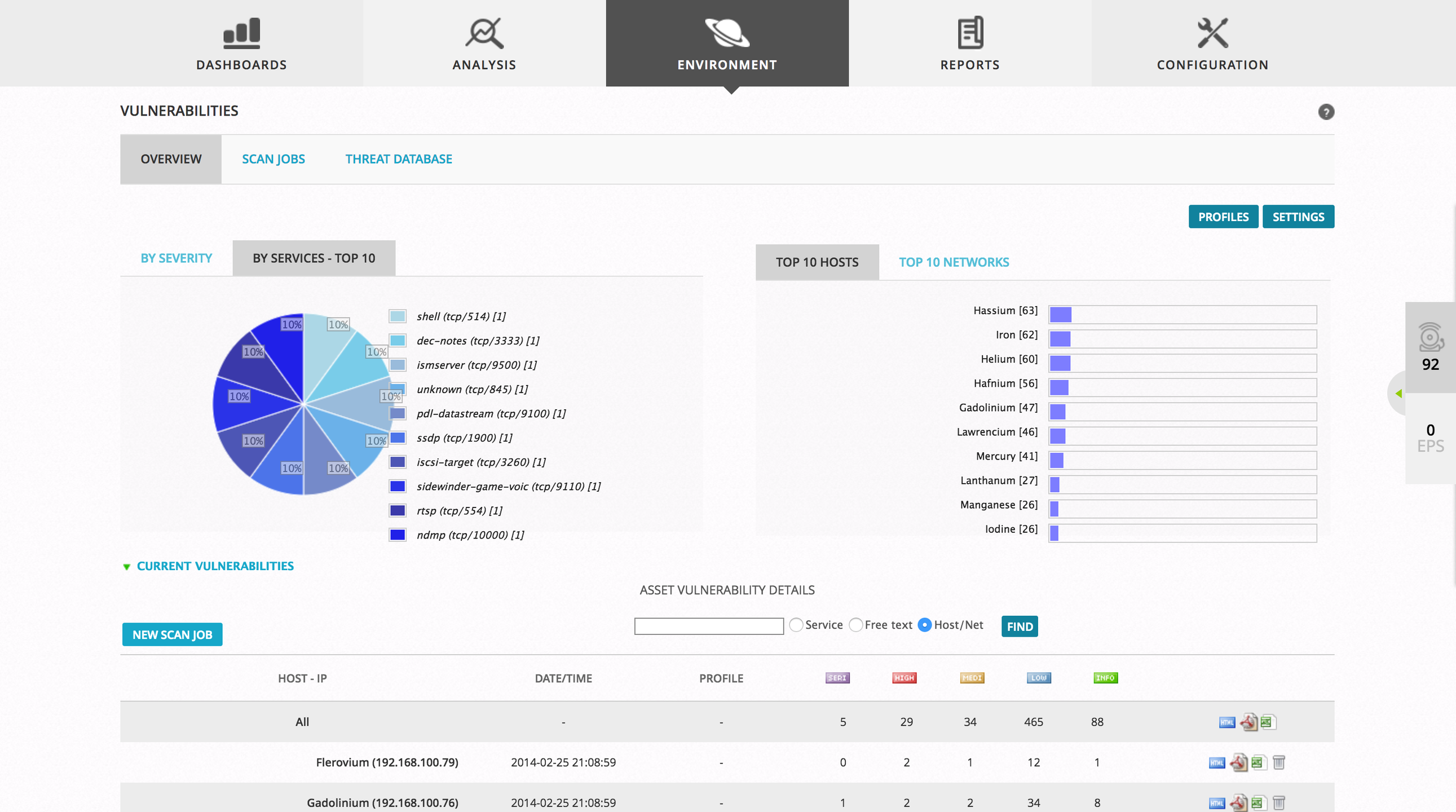
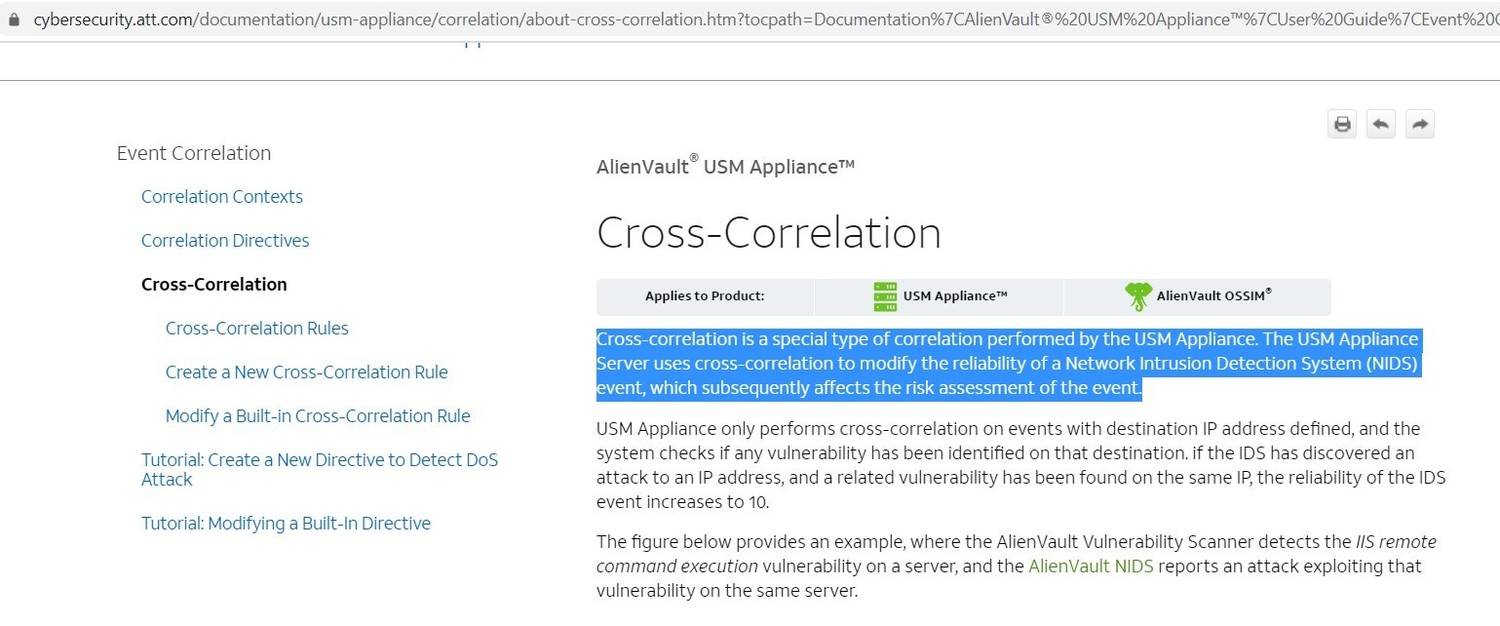
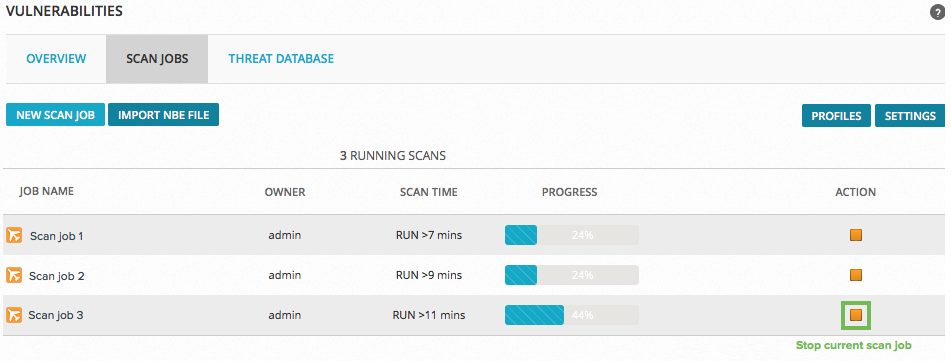
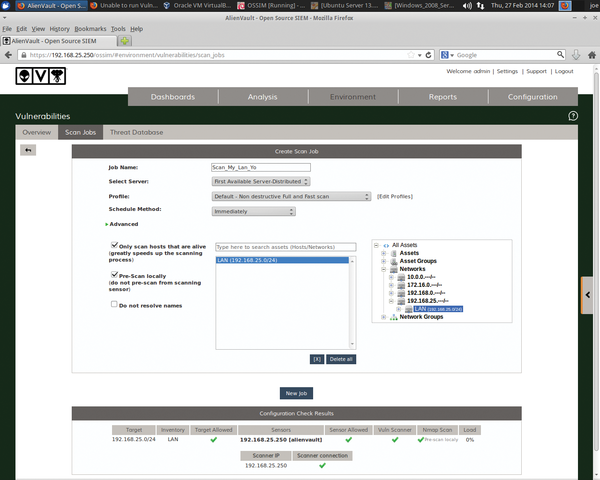
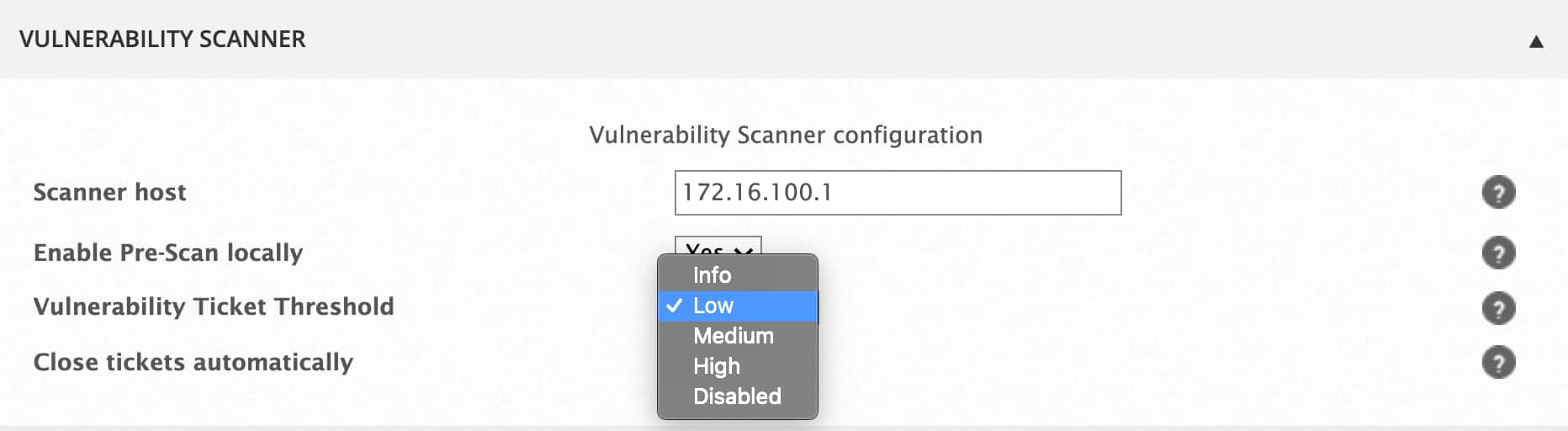
![project]Conduct Vulnerability Assessment using OSSIM and deal with incident tickets | by Takahiro Oda | Medium project]Conduct Vulnerability Assessment using OSSIM and deal with incident tickets | by Takahiro Oda | Medium](https://miro.medium.com/max/928/1*amil0A8LXeoXjItnHsxS6g.png)


![10 BEST External Vulnerability Scanner Tools [2022 SELECTIVE] 10 BEST External Vulnerability Scanner Tools [2022 SELECTIVE]](https://www.softwaretestinghelp.com/wp-content/qa/uploads/2021/09/Top-External-Vulnerability-Scanner-1.png)